Best Hardware Wallets 2025: Compare
Choosing the right air-gapped storage device is crucial for securing your cryptocurrency investments. This comprehensive comparison covers the top security solutions of 2025, analysing security features, supported cryptocurrencies, user experience, and value for money to help you make an informed decision.
Introduction
The cryptocurrency security landscape has evolved dramatically in 2025. Hardware wallets have become essential tools for anyone serious about protecting their digital assets. Cyber threats are more sophisticated. Exchange hacks continue to make headlines. The importance of self-custody through hardware wallets cannot be overstated. These devices provide the highest level of security by keeping private keys completely offline, away from internet-connected devices that could be compromised.
Hardware wallets represent the gold standard in cryptocurrency security. They offer protection that software wallets and exchange custody simply cannot match. By storing private keys on dedicated hardware devices with secure elements, these wallets create an impenetrable barrier between your cryptocurrency holdings and potential online threats. Leading manufacturers have continuously improved their offerings. They introduce features like larger screens, Bluetooth connectivity, and support for thousands of different cryptocurrencies whilst maintaining core security principles.
The market for hardware wallets has matured significantly. Established players like Ledger and Trezor are joined by innovative newcomers offering unique approaches to cryptocurrency security. From air-gapped devices that use QR codes for communication to card-based wallets that eliminate seed phrases entirely, the variety of options available in 2025 ensures there's a hardware wallet solution for every type of user and security preference.
The evolution of hardware wallet technology has brought improvements in user experience. Modern devices feature intuitive interfaces, mobile app integration, and streamlined setup processes. These make cryptocurrency security accessible to users of all technical levels. Advanced features like multi-signature support, passphrase protection, and integration with DeFi protocols have expanded the capabilities of these devices beyond simple storage to comprehensive cryptocurrency management tools.
Understanding the differences between these devices is crucial for making an informed decision. This decision should align with your security needs, technical comfort level, and cryptocurrency usage patterns. This comprehensive comparison examines the leading hardware wallets of 2025. We analyse their security features, supported cryptocurrencies, user experience, and value propositions to help you choose the perfect device for protecting your digital assets.
Why Secure Storage Is Essential in 2025
Cryptocurrency adoption is reaching new heights. Cyber threats are becoming more sophisticated. These devices have become indispensable for serious crypto investors and DeFi participants. They provide the highest level of security by keeping your private keys offline, away from internet-connected devices that could be compromised.
The offline storage market has evolved significantly. It offers diverse solutions from traditional USB devices to innovative card-based systems with advanced cryptographic security. Understanding the differences between these options is crucial for selecting the right security solution that meets your DeFi interaction needs, staking requirements, and budget constraints.
The cryptocurrency landscape in 2025 has witnessed unprecedented growth in both adoption and sophistication of security threats. Hardware wallets have emerged as the gold standard for cryptocurrency storage. They offer a perfect balance between security and usability. Unlike software wallets that store private keys on internet-connected devices, hardware wallets keep your keys isolated in secure elements. This makes them virtually immune to remote attacks, malware, and phishing attempts that have compromised billions of dollars in digital assets.
The evolution of hardware wallet technology has brought significant improvements in user experience, multi-chain support, and integration with decentralised finance protocols. Modern devices now support thousands of cryptocurrencies. They enable seamless interaction with DeFi applications. They provide intuitive interfaces that make secure storage accessible to users of all technical backgrounds. This democratisation of security has made it easier than ever to take full control of your digital assets whilst maintaining the highest levels of protection.
Key Benefits
- Offline Security: Private keys never leave the device, protecting against online attacks and smart contract exploits
- Multi-Currency Support: Store multiple cryptocurrencies, tokens, and DeFi assets on a single device
- Backup and Recovery: Secure wallet backup ensures funds can be recovered from any blockchain network
- Transaction Verification: Physical confirmation required for all transactions, including DeFi protocol interactions
- Long-term Storage: Ideal for holding cryptocurrency investments, staking rewards, and yield farming proceeds securely over time
Top Devices Comparison 2025
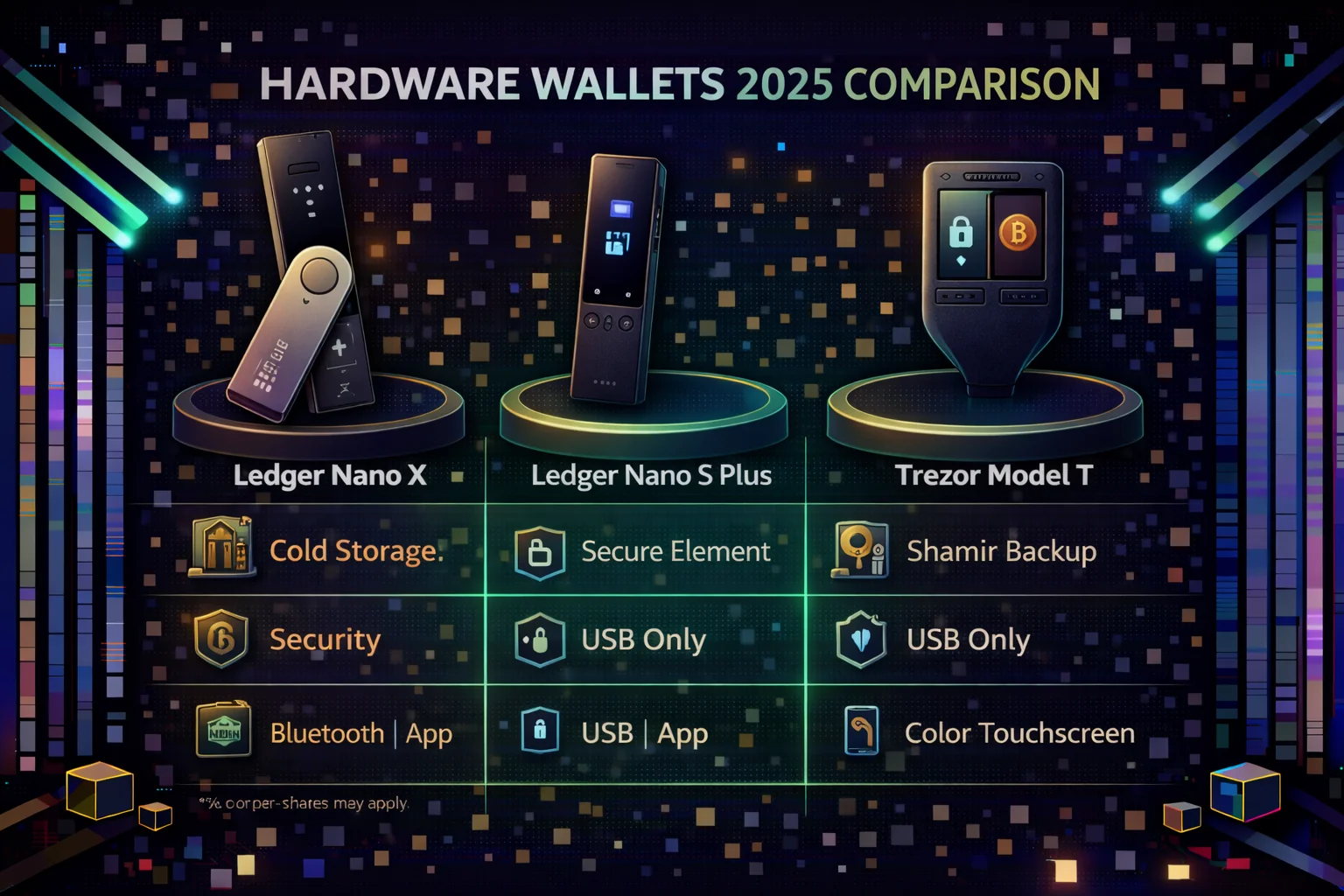
1. Nano wallet X - The Industry Standard
Price: $149 | Security Rating: 9.5/10 | Ease of Use: 8.5/10
The Ledger hardware X remains the gold standard for secure storage devices, offering unmatched security through its certified security module (CC EAL5+) and comprehensive cryptocurrency support. With over 5,500 supported assets, including DeFi tokens and Bluetooth connectivity, it provides the perfect balance of security and convenience for blockchain interactions.
Key Features:
- hardware security chip (CC EAL5+ certified)
- 5,500+ supported cryptocurrencies
- Bluetooth connectivity for mobile use
- 100 apps can be installed simultaneously
- Battery life: several hours of active use
- Ledger Live app integration
Pros:
- Highest security standards in the industry
- Extensive cryptocurrency support
- Regular firmware updates and security patches
- Strong reputation and track record
- Excellent mobile app integration
Cons:
- Higher price point
- Past data breach (customer information, not funds)
- Closed-source firmware
- Small screen can be challenging for some users
Best For: Serious investors with diverse crypto portfolios who prioritise maximum security and don't mind paying premium prices.
Get Ledger device X with Exclusive Bonuses →
2. Trezor Model T - Open Source Pioneer
Price: $219 | Security Rating: 9.0/10 | Ease of Use: 9.0/10
The Trezor Model T stands out as the premium open-source security device, featuring a full-colour touchscreen and support for advanced features like Shamir Backup. Its transparent, open-source approach appeals to users who value code auditability, community-driven development, and decentralised governance principles.
Key Features:
- Full-colour touchscreen interface
- 1,600+ supported cryptocurrencies
- Shamir Backup (advanced seed splitting)
- Passphrase protection
- Open-source firmware and software
- MicroSD card slot for additional features
Pros:
- Completely open-source (hardware and software)
- Intuitive touchscreen interface
- Advanced security features (Shamir Backup)
- Strong privacy focus
- Excellent build quality
Cons:
- Most expensive option
- Fewer supported cryptocurrencies than Ledger
- No Bluetooth connectivity
- Larger form factor
Best For: Privacy-conscious users who value open-source transparency and don't mind paying premium for advanced features.
Get Trezor Model T with Exclusive Bonuses →
3. Keystone Pro - Air-Gapped Security
Price: $159 | Security Rating: 9.0/10 | Ease of Use: 7.0/10
The Keystone Pro offers maximum security through its 100% air-gapped design, using QR codes for all communication. This approach eliminates USB and Bluetooth attack vectors, making it ideal for users with the highest security requirements.
Key Features:
- 4-inch touchscreen display
- 100% air-gapped (QR code communication only)
- Open-source firmware
- Multi-signature support
- Shamir Secret Sharing
- Built-in camera for QR scanning
Pros:
- Maximum security through air-gapped design
- Large, clear touchscreen
- No USB or wireless attack vectors
- Advanced multi-signature features
- Competitive pricing
Cons:
- QR code workflow can be cumbersome
- Limited cryptocurrency support
- No Bluetooth connectivity
- Larger form factor
Best For: Privacy-conscious users who value open-source solutions and want the most advanced security features available.
Get Trezor Model T with Special Offers →
3. Tangem Storage Solution - Revolutionary Card Design
Price: $55-75 | Security Rating: 8.5/10 | Ease of Use: 9.5/10
Tangem revolutionises hardware storage solution design with its credit card-sized form factor and NFC tap-to-sign functionality. This innovative approach eliminates batteries, screens, and cables while maintaining high security standards through certified secure elements and advanced cryptographic protocols for blockchain transactions.
Key Features:
- Credit card form factor
- NFC tap-to-sign transactions
- No batteries, screens, or cables required
- Certified secure element (CC EAL6+)
- Water and dust resistant
- Backup cards included in sets
Pros:
- Most portable and convenient design
- Excellent value for money
- No charging required
- Intuitive NFC operation
- Durable construction
- Built-in backup system
Cons:
- Limited cryptocurrency support
- Newer technology with shorter track record
- Requires NFC-enabled smartphone
- Less advanced features compared to traditional wallets
Best For: Users who prioritise convenience and portability while maintaining strong security for major cryptocurrencies.
Get Tangem Wallet with Exclusive Discounts →
4. Keystone Pro - Air-Gapped Security
Price: $179 | Security Rating: 9.5/10 | Ease of Use: 8.0/10
Keystone Pro takes security to the extreme with its air-gapped design, using QR codes for all communication with blockchain networks. This approach eliminates any possibility of digital connection compromise while providing a large touchscreen for enhanced usability in DeFi protocol interactions and multi-signature transactions.
Key Features:
- 4-inch touchscreen display
- 100% air-gapped (QR code communication)
- Open-source firmware
- Shamir Secret Sharing support
- Multi-signature wallet support
- Removable battery
Pros:
- Maximum security through air-gapped design
- Large, easy-to-read screen
- Open-source and auditable
- Advanced features for power users
- No physical connection vulnerabilities
Cons:
- More complex setup and usage
- QR code scanning can be cumbersome
- Higher learning curve
- Limited mobile app ecosystem
Best For: Security-focused power users who want maximum protection and don't mind additional complexity.
Get Keystone Pro with Special Pricing →
5. Trezor One - Budget-Friendly Security
Price: $69 | Security Rating: 8.0/10 | Ease of Use: 8.0/10
The Trezor One offers essential security device functionality at an accessible price point. Whilst lacking some advanced features of its premium counterpart, it provides solid security and open-source transparency for budget-conscious users.
Key Features:
- OLED display with physical buttons
- 1,600+ supported cryptocurrencies
- Open-source firmware
- Passphrase protection
- Recovery seed backup
- Web-based interface
Pros:
- Most affordable from reputable brand
- Open-source transparency
- Proven track record
- Simple, reliable operation
- Good cryptocurrency support
Cons:
- Small screen and basic interface
- No touchscreen or advanced features
- Limited to basic security functions
- No Bluetooth connectivity
Best For: Beginners and budget-conscious users who want reliable security without premium features.

Detailed Feature Comparison
Security Features Comparison
| Feature | Nano wallet X | Trezor Model T | Tangem | Keystone Pro | Trezor One |
|---|---|---|---|---|---|
| Secure Element | CC EAL5+ | No | CC EAL6+ | No | No |
| Open Source | Partial | Full | No | Full | Full |
| PIN Protection | Yes | Yes | Yes | Yes | Yes |
| Passphrase Support | Yes | Yes | No | Yes | Yes |
| Shamir Backup | No | Yes | No | Yes | No |
| Multi-Signature Support | Yes | Yes | No | Yes | Yes |
| Recovery Seed Length | 12/24 words | 12/24 words | Card-based | 12/24 words | 12/24 words |
| Physical Security | Tamper-evident | Tamper-evident | Tamper-resistant | Tamper-evident | Tamper-evident |
Connectivity and Usability
| Feature | Ledger device X | Trezor Model T | Tangem | Keystone Pro | Trezor One |
|---|---|---|---|---|---|
| Screen Type | OLED | colour Touch | None | 4" colour Touch | OLED |
| Connectivity | USB-C, Bluetooth | USB-C | NFC | QR Codes | Micro-USB |
| Mobile Support | Excellent | Limited | Excellent | Good | Limited |
| Battery Required | Yes | No | No | Yes | No |
| Setup Difficulty | Easy | Easy | Very Easy | Moderate | Easy |
Cryptocurrency Support
- Nano wallet X: 5,500+ cryptocurrencies including Bitcoin, Ethereum, and virtually all major altcoins
- Trezor Model T: 1,600+ cryptocurrencies with strong support for major coins and tokens
- Tangem: 6,000+ cryptocurrencies with focus on major assets and popular DeFi tokens
- Keystone Pro: 1,000+ cryptocurrencies with emphasis on Bitcoin and Ethereum ecosystems
- Trezor One: 1,600+ cryptocurrencies, same as Model T but with basic interface
Choosing the Right hardware device
For Beginners
Recommended: Tangem Wallet
The Tangem wallet offers the easiest entry point into cold storage device security. Its card-based design eliminates complexity while providing strong security through certified secure elements. The NFC tap-to-sign functionality makes transactions intuitive, and the affordable price makes it accessible for newcomers.
For Serious Investors
Recommended: Ledger hardware X
With the broadest cryptocurrency support and proven security track record, the Ledger Nano X is ideal for investors with diverse portfolios. Its Bluetooth connectivity enables convenient mobile use while maintaining the highest security standards through certified secure elements.
For Privacy Advocates
Recommended: Trezor Model T
The fully open-source nature of Trezor devices appeals to users who want complete transparency in their security solutions. The Model T's advanced features, like Shamir Backup and touchscreen interface, provide both security and usability for privacy-focused users.
For Maximum Security
Recommended: Keystone Pro
The air-gapped design of Keystone Pro eliminates any possibility of digital connection compromise. Whilst more complex to use, it provides the ultimate security for users storing significant amounts of cryptocurrency who prioritise protection above convenience.
For Budget-Conscious Users
Recommended: Trezor One
The Trezor One provides essential security device protection at the most affordable price from a reputable manufacturer. Whilst lacking advanced features, it offers solid protection and open-source transparency for users with basic security needs.
Security Best Practices
Initial Setup
- Always buy directly from the manufacturer or authorised retailers
- Verify the device hasn't been tampered with upon arrival
- Generate your recovery phrase on the device, never use pre-generated seeds
- Write down your recovery phrase on paper, never store it digitally
- Test your backup by recovering a small amount before storing large sums
Ongoing Security
- Keep your firmware updated with the latest security patches
- Use strong, unique PINs and consider passphrase protection
- Store your mnemonic phrase in multiple secure, separate locations
- Never enter your backup words on any computer or online service
- Consider using multiple cold storage devices for extensive holdings
Common Mistakes to Avoid
- Buying from unauthorised sellers or second-hand markets
- Storing seed phrases digitally or in cloud services
- Using the same PIN for multiple devices
- Ignoring firmware updates
- Not testing recovery procedures
- Sharing device access or seed phrases with others
Future of Crypto Security
The cold storage device industry continues to evolve with new technologies and form factors. Emerging trends include biometric authentication, improved mobile integration, and enhanced user interfaces. As cryptocurrency adoption grows, we anticipate seeing more innovative designs that strike a balance between security and usability.
Multi-signature support and integration with DeFi protocols are becoming increasingly important features. The rise of NFTs and new blockchain networks also drives demand for broader cryptocurrency support across all security wallet manufacturers.
Emerging Technologies
- Biometric Authentication: Fingerprint and facial recognition integration
- Wireless Charging: Elimination of charging cables for battery-powered devices
- Enhanced Displays: Larger, higher-resolution screens for better user experience
- Multi-Chain Support: Native support for emerging blockchain networks
- DeFi Integration: Direct interaction with decentralised finance protocols
Advanced Security Features and Professional Applications
Multi-Signature and Enterprise Security
Professional cryptocurrency management requires sophisticated security architectures that go beyond single-device protection to include multi-signature capabilities, enterprise-grade access controls, and comprehensive audit trails. Advanced hardware wallet implementations support multi-signature configurations where multiple devices must approve transactions, providing protection against single points of failure and enabling sophisticated corporate governance structures for cryptocurrency holdings.
Enterprise security features include integration with corporate security frameworks, comprehensive reporting capabilities, and advanced authentication mechanisms that meet institutional security requirements. Professional applications include treasury management, corporate cryptocurrency holdings, and institutional custody solutions that require the highest levels of security while maintaining operational efficiency and regulatory compliance across diverse business requirements and security standards.
Integration with DeFi and Advanced Protocols
Modern hardware wallets provide sophisticated integration capabilities with decentralised finance protocols, enabling secure participation in yield farming, liquidity provision, and other advanced cryptocurrency strategies. These integrations maintain the security benefits of hardware wallet storage while enabling users to participate in complex DeFi activities through secure transaction signing and comprehensive protocol interaction capabilities.
Advanced protocol support includes integration with emerging blockchain networks, cross-chain functionality, and sophisticated smart contract interaction capabilities that enable users to participate in the latest cryptocurrency innovations while maintaining security. Professional users benefit from comprehensive transaction verification, detailed protocol analysis, and advanced risk assessment tools that ensure secure participation in complex cryptocurrency strategies and emerging protocol developments.
Future-Proofing and Technology Evolution
Hardware wallet technology continues evolving to address emerging security threats, support new blockchain networks, and integrate with advancing cryptocurrency technologies. Future-proofing considerations include quantum-resistant cryptography, support for emerging consensus mechanisms, and integration with next-generation blockchain technologies that ensure long-term security and compatibility with evolving cryptocurrency ecosystems.
Technology evolution includes enhanced user interfaces, improved mobile integration, and advanced connectivity options that make hardware wallets more accessible while maintaining security standards. Professional development includes integration with emerging technologies, support for new cryptocurrency standards, and comprehensive upgrade pathways that ensure hardware wallet investments remain valuable and secure as cryptocurrency technology continues advancing and evolving.
Professional Security Analysis and Enterprise Applications
Institutional-Grade Security Frameworks
Professional cryptocurrency management requires hardware wallet solutions that meet institutional security standards through comprehensive risk assessment, multi-signature implementations, and enterprise-grade operational procedures. Institutional users evaluate hardware wallets based on security certifications, audit histories, and compliance with regulatory frameworks that govern professional cryptocurrency custody operations.
Enterprise security considerations encompass physical security protocols, access control mechanisms, and disaster recovery procedures that protect against both technical and operational risks. Professional users implement comprehensive security frameworks that include hardware wallet integration with existing security infrastructure, staff training programs, and regular security assessments that maintain institutional standards.
Advanced Multi-Signature and Custody Solutions
Sophisticated cryptocurrency custody strategies leverage hardware wallets within multi-signature configurations that distribute risk across multiple devices and stakeholders while maintaining operational efficiency and security standards. Multi-signature implementations require careful consideration of threshold requirements, key distribution strategies, and operational procedures that balance security with accessibility.
Professional custody solutions integrate hardware wallets with specialised software platforms that provide audit trails, compliance reporting, and automated security monitoring capabilities. These integrated solutions enable institutional users to maintain custody control while meeting regulatory requirements and operational standards necessary for professional cryptocurrency management.
Emerging Technologies and Future Developments
Hardware wallet technology continues to evolve through integration of advanced security features, improved user interfaces, and enhanced connectivity options that address emerging threats and user requirements. Future developments include quantum-resistant cryptography, biometric authentication systems, and advanced communication protocols that will define the next generation of cryptocurrency security devices.
Innovation trends encompass integration with decentralised identity systems, enhanced mobile connectivity, and advanced privacy features that expand hardware wallet capabilities while maintaining security standards. Professional users monitor these developments to ensure their security strategies remain current with technological advances and emerging threat vectors.
Advanced Security Considerations and Professional Implementation
Enterprise Security Protocols and Multi-Signature Configurations
Professional cryptocurrency security requires implementing multi-signature configurations, hardware security modules, and sophisticated backup strategies that protect against various attack vectors while maintaining operational efficiency. Enterprise security implementations include comprehensive key management policies, regular security audits, and employee training programs that minimise human error risks and ensure consistent application of security best practices.
Advanced security configurations include geographic distribution of backup materials, time-locked transactions, and social recovery mechanisms that ensure asset protection while maintaining accessibility for legitimate use. Professional users employ multiple security layers that address physical security, digital security, and operational security requirements for comprehensive cryptocurrency asset protection and risk management.
Institutional Custody Solutions and Compliance Frameworks
Institutional cryptocurrency custody requires comprehensive compliance frameworks that address regulatory requirements, fiduciary responsibilities, and operational risk management while maintaining the security benefits of hardware wallet technology. Professional custody solutions include segregated storage systems, comprehensive insurance coverage, and sophisticated operational procedures that meet traditional financial industry requirements.
Compliance frameworks enable pension funds, insurance companies, and asset management firms to utilise hardware wallet technology through established compliance procedures and professional risk management systems that satisfy regulatory oversight requirements while maintaining the security and control benefits that make hardware wallets attractive for institutional cryptocurrency storage and management operations.
Professional hardware wallet implementation requires comprehensive operational procedures, systematic security protocols, and advanced risk management frameworks that ensure optimal cryptocurrency security while maintaining operational efficiency and regulatory compliance for institutional cryptocurrency operations and professional digital asset management that demands the highest security standards and operational excellence through systematic implementation and professional security management designed for enterprise cryptocurrency storage and institutional treasury operations.
Technology Evolution and Future Security Innovations
Hardware wallet technology continues advancing with biometric authentication systems, enhanced connectivity options, and improved user interfaces that maintain security whilstenhancing usability for professional cryptocurrency management. Future innovations include quantum-resistant cryptographic algorithms, advanced tamper detection mechanisms, and sophisticated backup systems that ensure long-term security against evolving threats and technological developments.
Emerging security technologies include integration with decentralised identity systems, enhanced privacy features, and sophisticated multi-party computation capabilities that enable advanced security configurations while maintaining user control and operational flexibility. Professional users benefit from continuous security improvements, enhanced compatibility with emerging protocols, and advanced features that support sophisticated cryptocurrency operations and institutional security requirements.
Operational Excellence and Professional Best Practices
Professional hardware wallet operations require systematic procedures for device initialization, backup management, and security maintenance that ensure consistent protection while minimising operational risks and human error factors. Best practices include comprehensive documentation, regular security reviews, and systematic training programs that maintain security standards while enabling efficient cryptocurrency operations and professional asset management.
Operational excellence includes implementing comprehensive monitoring systems, maintaining detailed audit trails, and developing sophisticated contingency plans that address various failure scenarios while ensuring business continuity and asset protection. Professional operations benefit from systematic procedures, comprehensive risk management, and advanced operational frameworks that enable sustainable cryptocurrency security and long-term asset protection through professional hardware wallet implementation and institutional security management excellence.
Conclusion
Choosing the right cold storage solution depends on your specific needs, technical expertise, and budget. The Ledger Nano X offers the best overall combination of security and features for most users, while the Tangem wallet provides unmatched convenience for beginners. Privacy advocates will appreciate the open-source transparency of Trezor devices, and security-focused users should consider the air-gapped design of Keystone Pro.
Regardless of which device you choose, the most important step is actually using one. The security benefits of cold storage devices far outweigh the minor inconveniences, and proper setup with secure backup procedures will protect your cryptocurrency investments for years to come.
Remember that these devices are just one part of a comprehensive security strategy. Combine your cold storage solution with strong operational security practices, regular software updates, and careful attention to emerging threats to maintain the highest level of protection for your digital assets.
The hardware wallet market continues to evolve rapidly, with manufacturers constantly improving security features, user experience, and blockchain compatibility. As the cryptocurrency ecosystem matures and institutional adoption increases, hardware wallets will play an increasingly important role in securing digital assets. The investment in a quality hardware wallet today not only protects your current holdings but also positions you for safe participation in future developments in decentralised finance, NFTs, and emerging blockchain technologies.
Whether you're a beginner taking your first steps into cryptocurrency self-custody or an experienced user looking to upgrade your security setup, the hardware wallets reviewed in this comparison represent the best options available in 2025. Take the time to evaluate your specific needs, consider your technical comfort level, and choose the device that best aligns with your security requirements and usage patterns. Your future self will thank you for making the investment in proper cryptocurrency security.
Hardware wallet evaluation requires understanding security chip technology, firmware update mechanisms, and physical design factors that determine long-term protection effectiveness. Different hardware wallet manufacturers employ varying approaches to cold storage security, with each device offering unique advantages for specific threat models and usage scenarios that align with individual security requirements and technical expertise levels.
Sources & References
Frequently Asked Questions
- What is the best cold storage device in 2025?
- Ledger Nano X is the best overall crypto wallet with extensive coin support, Bluetooth connectivity, and proven security. Trezor Model T offers excellent open-source security, while Tangem provides the most user-friendly card-based design. Choose based on your priorities: features (Ledger), transparency (Trezor), or simplicity (Tangem).
- Are hardware wallets worth it?
- Yes, cold wallets are essential for anyone holding significant cryptocurrency amounts. They provide the highest security by keeping private keys offline, protecting against hacks, malware, and phishing. The $50-150 investment is worthwhilst for holdings above $1000.
- Can hardware wallets be hacked?
- Hardware wallets are extremely difficult to hack due to secure element chips and offline storage. Whilst theoretical vulnerabilities exist, no major hardware device has been successfully hacked remotely. The main risks are physical theft (mitigated by PIN) and phishing attacks (always verify addresses).
- Do I need multiple hardware wallets?
- Having 2-3 hardware wallets is recommended for redundancy and security. Use one as your primary wallet, keep a backup with the same seed phrase in a secure location, and optionally use a different brand as a secondary wallet for diversification. This protects against device failure or loss.
- What happens if I lose my security wallet?
- Your crypto is safe if you have your recovery seed phrase (12-24 words). Purchase a new cold storage device and restore using your seed phrase. This is why securely storing your recovery phrase is crucial - keep it offline in a fireproof safe or safety deposit box. Never store it digitally or share it with anyone.
- Which cryptocurrencies do devices support?
- Most devices support major cryptocurrencies like Bitcoin, Ethereum, and thousands of ERC-20 tokens. Ledger supports 5,500+ coins, Trezor supports 1,800+, and Tangem supports 6,000+ assets. Check the manufacturer's website for specific coin support before purchasing, especially if you hold less common altcoins.